Having completed a minimal install there are a few things that need to be tweaked a bit in order to keep it that way.
You can reduce the amount of disk space used by keeping the number of additional packages that are installed to a minimum but configuring APT so that it does not install the recommended or suggested packages. To do this on recent Debian distributions (e.g. squeeze wheezy) you need to login as root and use the following command to create a new configuration file.
# vi /etc/apt/apt.conf.d/10norecommends
Then add the following two lines.
APT::Install-Recommends "0"; APT::Install-Suggests "0";
Even though it doesn’t seem like it is always necessary on a desktop system, I tend to install openssh server on all my Linux boxes, and not just the servers – it is particularly useful when setting up a new system as once openssh-server is installed you can connect to the machine being configured from another working desktop and just copy and paste the commands you need to run from the web browser or documentation into the terminal window.
# apt-get install openssh-server Reading package lists... Done Building dependency tree Reading state information... Done The following extra packages will be installed: libbsd0 libedit2 openssh-client Suggested packages: ssh-askpass libpam-ssh keychain monkeysphere rssh molly-guard Recommended packages: openssh-blacklist openssh-blacklist-extra ncurses-term The following NEW packages will be installed: libbsd0 libedit2 openssh-client openssh-server 0 upgraded, 4 newly installed, 0 to remove and 0 not upgraded. Need to get 1,521 kB of archives. After this operation, 3,540 kB of additional disk space will be used. Do you want to continue [Y/n]? Y : : : Setting up openssh-client (1:6.0p1-4+deb7u1) ... Setting up openssh-server (1:6.0p1-4+deb7u1) ... Creating SSH2 RSA key; this may take some time ... Creating SSH2 DSA key; this may take some time ... Creating SSH2 ECDSA key; this may take some time ... [ ok ] Restarting OpenBSD Secure Shell server: sshd. : : : #
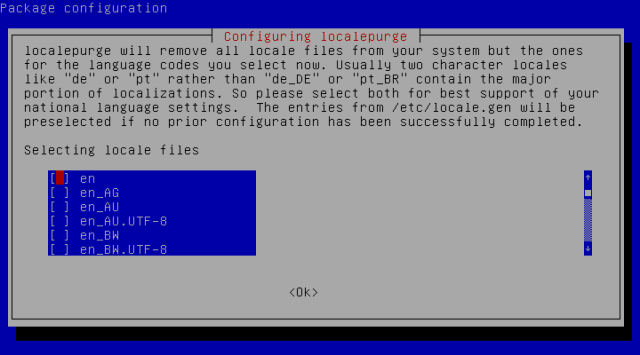
To remove any unnecessary locale support files that are installed to support other languages you will need a utility called localepurge – you only need to run this once as after it is installed it will run automatically when ever you install any additional packages.
# apt-get install localepurge Reading package lists… Done Building dependency tree Reading state information… Done Suggested packages: debfoster deborphan bleachbit The following NEW packages will be installed: localepurge 0 upgraded, 1 newly installed, 0 to remove and 0 not upgraded. Need to get 45.9 kB of archives. After this operation, 88.1 kB of additional disk space will be used. : : : Fetched 45.9 kB in 0s (95.6 kB/s) Preconfiguring packages …
When it is installed localepurge will ask you to select the files that should be removed by asking you to select which locales you want to use. Since I’m in the UK I actually deselect the generic english and only select en_GB and en_GB.UTF-8, I’m not sure if deselecting the generic english locale actually causes any additional files to be purged from the system, but it doesn’t seem to cause any problems.

: : : Setting up localepurge (0.6.3+deb7u1) … Creating config file /etc/locale.nopurge with new version
Then remove any locale specific files that have already been installed.
# localepurge localepurge: Disk space freed in /usr/share/locale: 52424 KiB localepurge: Disk space freed in /usr/share/man: 3744 KiB Total disk space freed by localepurge: 56168 KiB
To have the system automatically retrieve the date and time from the internet you need to install ntpdate this will set the time and date automatically when the system boots.
# apt-get install ntpdate Reading package lists... Done Building dependency tree Reading state information... Done Recommended packages: lockfile-progs The following NEW packages will be installed: ntpdate 0 upgraded, 1 newly installed, 0 to remove and 0 not upgraded. Need to get 80.5 kB of archives. After this operation, 224 kB of additional disk space will be used. : : : Setting up ntpdate (1:4.2.6.p5+dfsg-2) ... localepurge: Disk space freed in /usr/share/locale: 0 KiB localepurge: Disk space freed in /usr/share/man: 0 KiB Total disk space freed by localepurge: 0 KiB
Finally to protect the system I enable the firewall and configure it to only allow incoming connections to known ports – at this point we have only installed openssh-server so should only need to allow incoming ssh connections from the local subnet.
# apt-get install ufw Reading package lists... Done Building dependency tree Reading state information... Done The following extra packages will be installed: mime-support python python-minimal python2.7 python2.7-minimal Suggested packages: python-doc python-tk python2.7-doc binutils binfmt-support Recommended packages: file The following NEW packages will be installed: mime-support python python-minimal python2.7 python2.7-minimal ufw 0 upgraded, 6 newly installed, 0 to remove and 0 not upgraded. Need to get 4,827 kB of archives. After this operation, 15.7 MB of additional disk space will be used. Do you want to continue [Y/n]? Y : : : Setting up ufw (0.31.1-2) ... Creating config file /etc/ufw/before.rules with new version Creating config file /etc/ufw/before6.rules with new version Creating config file /etc/ufw/after.rules with new version Creating config file /etc/ufw/after6.rules with new version
To set up the firewall, begin by denying all incoming connections, then configure it to allow connections from your local subnet to port 22 using TCP. This will allow machines on your local network to connect to using ssh.
Note – Assuming that you are using a 24 bit subnet mask (255.255.255.0) then you will need to substitute the first three octets of your network address for nnn.nnn.nnn in the commands below.
# ufw default deny incoming Default incoming policy changed to 'deny' (be sure to update your rules accordingly) # ufw allow from nnn.nnn.nnn.0/24 to any port 22 proto tcp Rules updated # ufw enable Command may disrupt existing ssh connections. Proceed with operation (y|n)? y Firewall is active and enabled on system startup
Check that the firewall is configured and running…
# ufw status Status: active To Action From -- ------ ---- 22/tcp ALLOW 192.168.16.0/24
To reduce the load on the system I disable logging, there are pros and cons to this but I know I’m very unlikely to ever review the log files!
# ufw logging off Logging disabled
And that is all there is to it… For a desktop system you can continue by installing MATE or XFCE.

Very well outlined. Extremely easy to follow
ntpdate is deprecated. Please use sntp instead for manual or scripted NTP queries/syncs.
mike632t: Not only deprecated but not needed at all if you are installing Debian (Buster) !! (I need to update the post when I get time).